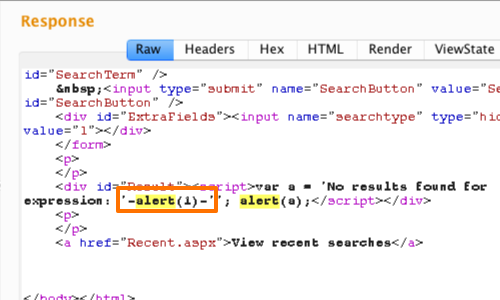
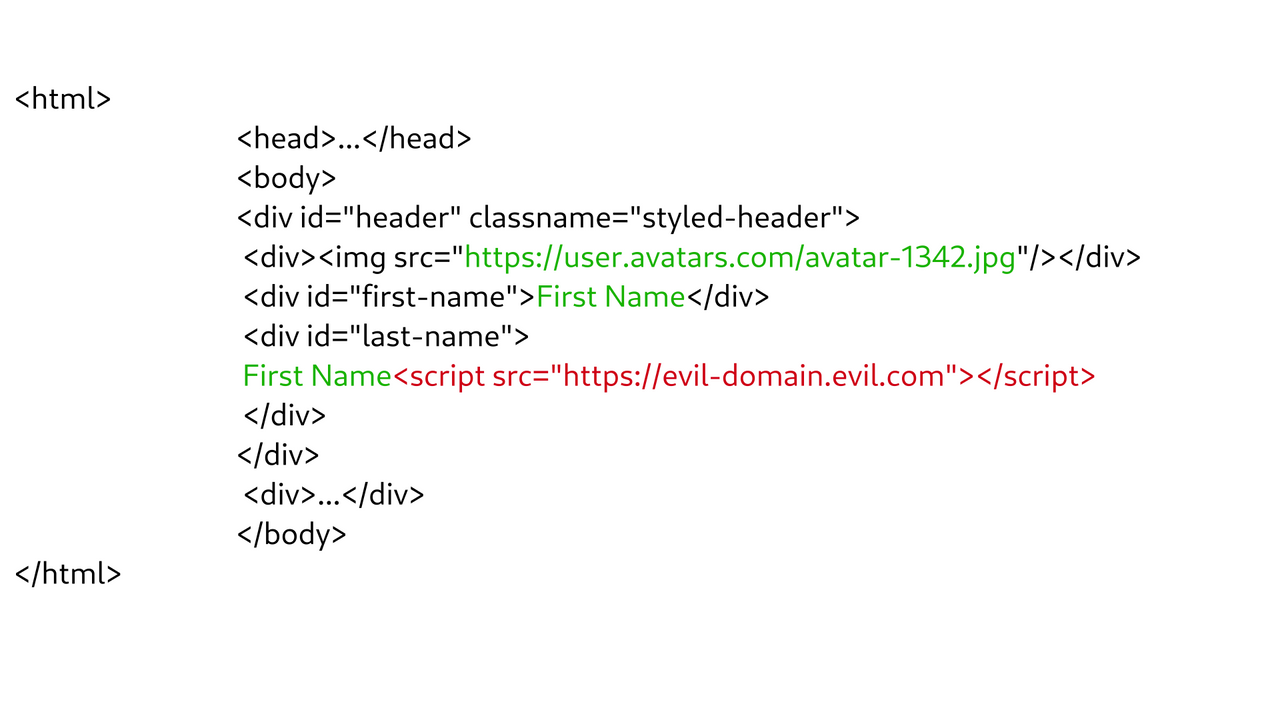
javascript - XSS - is it dangerous that innerText string can be HTML elements: script, div etc? - Stack Overflow
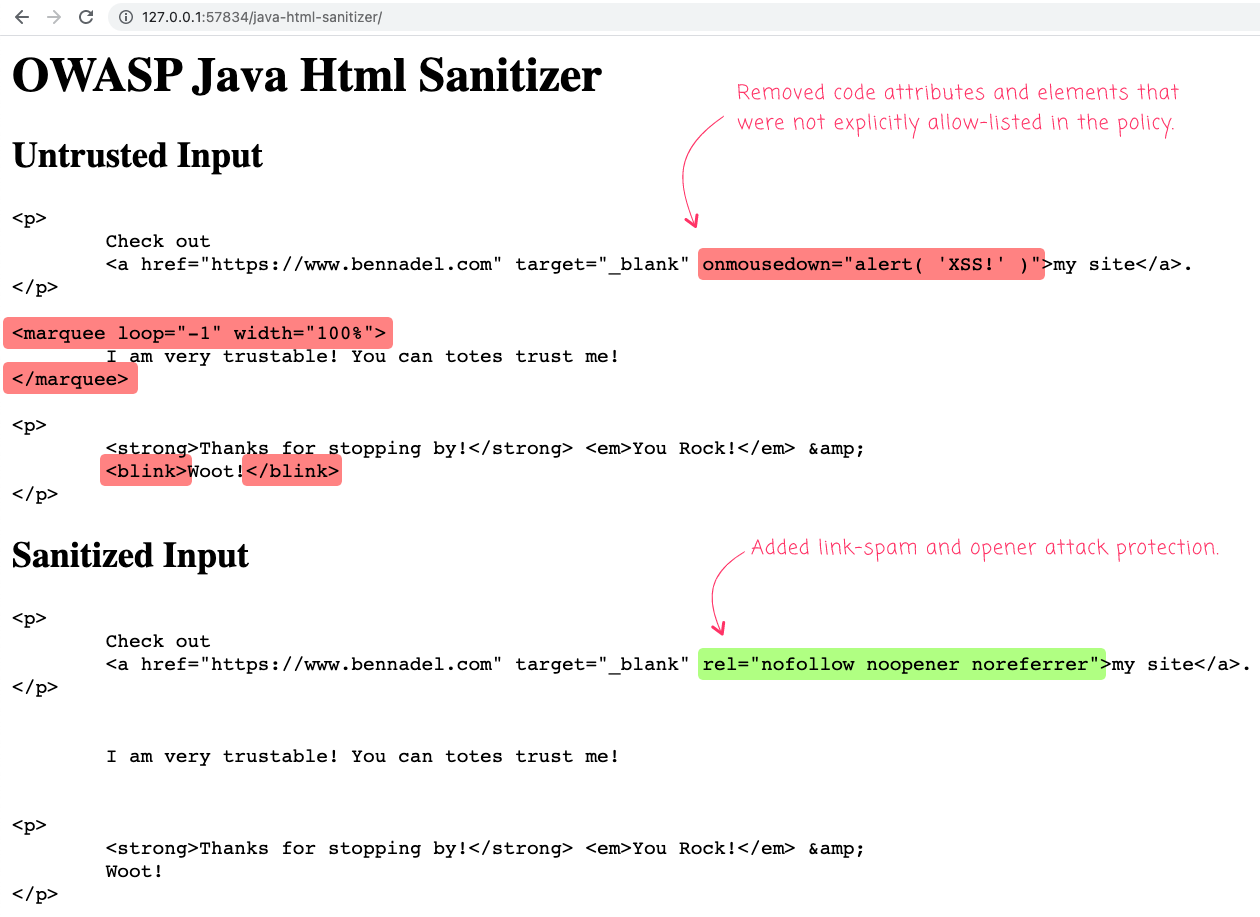
Using The OWASP Java HTML Sanitizer In Lucee CFML 5.3.7.48 To Sanitize HTML Input And Prevent XSS Attacks
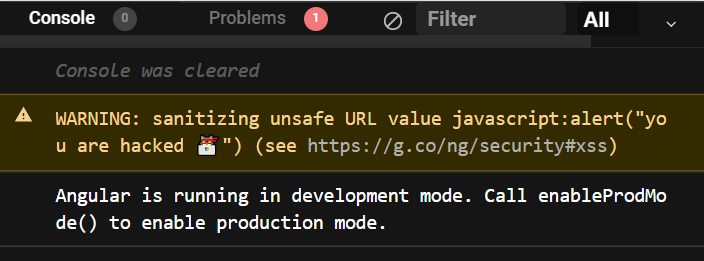
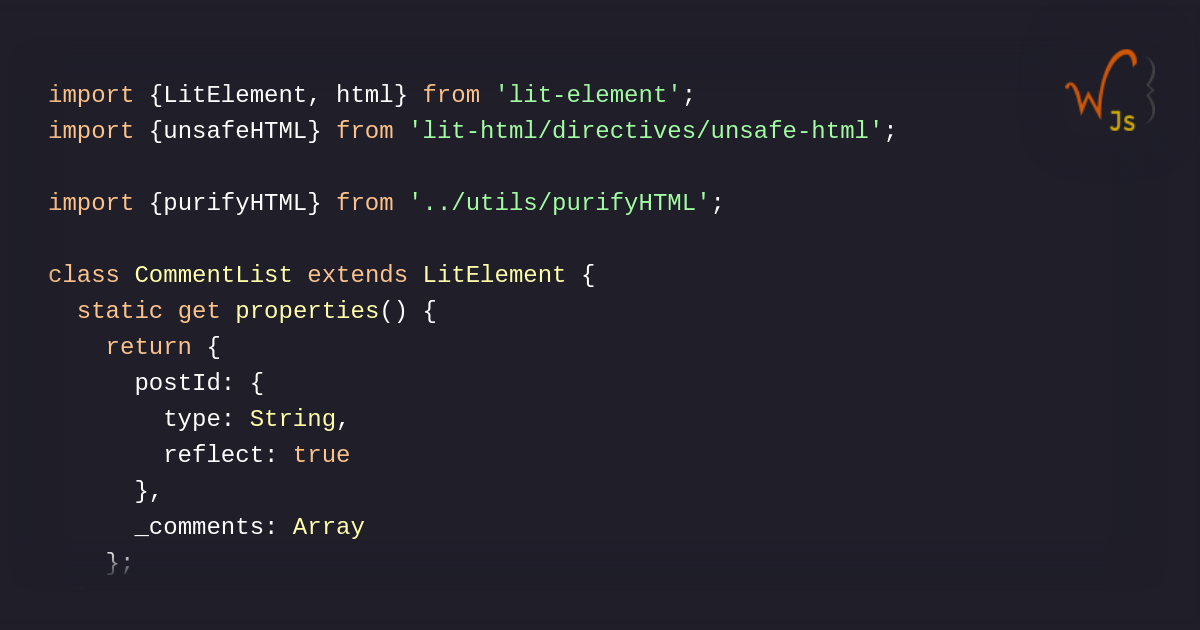
JavaScript — Securely Sanitizing User Input with Tagged Templates to prevent XSS attacks | by D Patel | Aug, 2023 | Medium
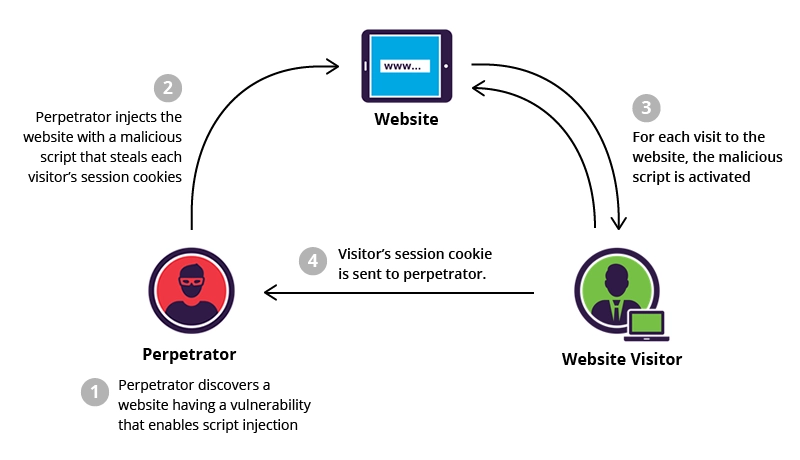
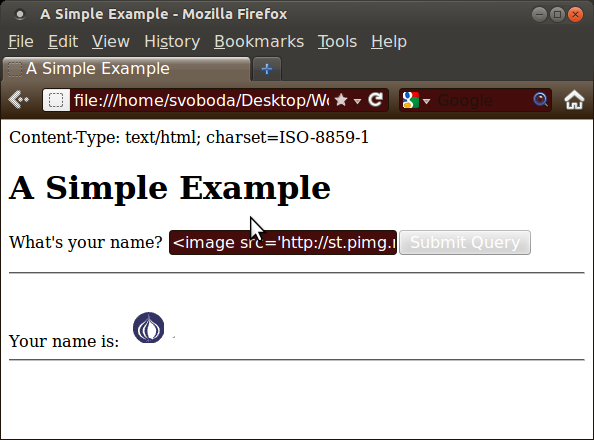
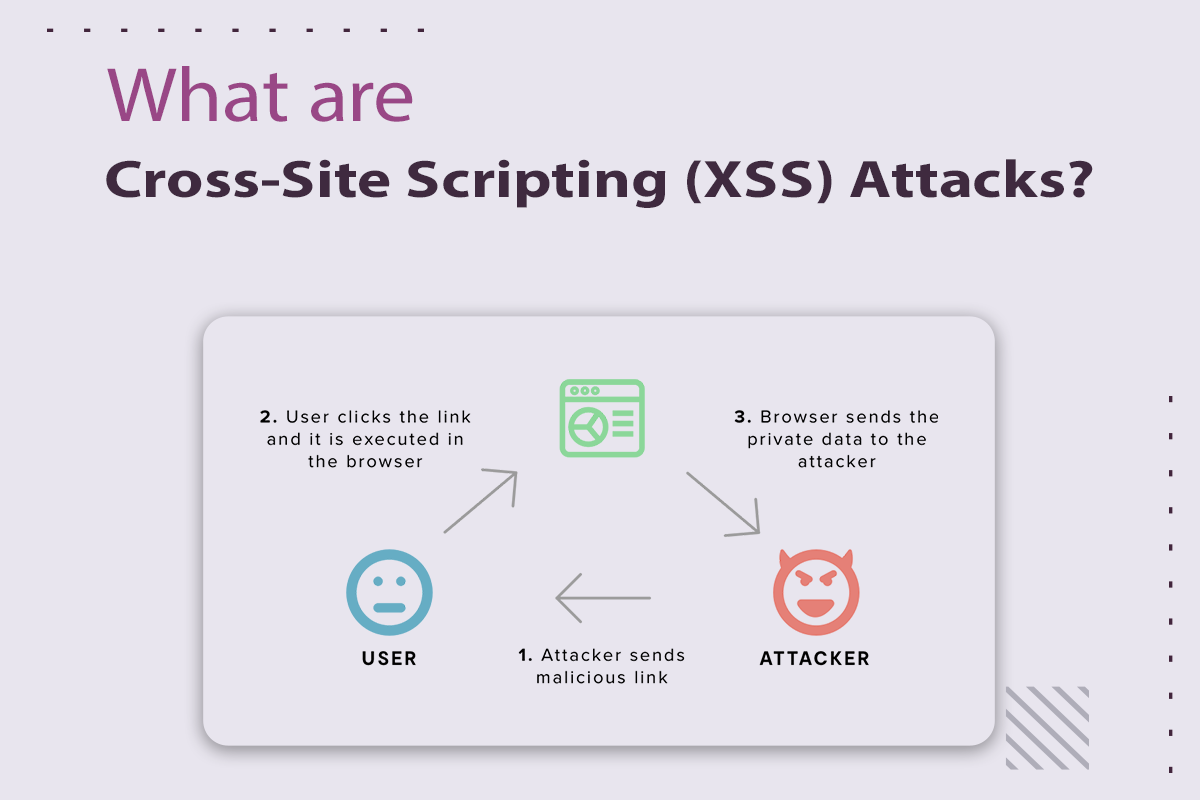
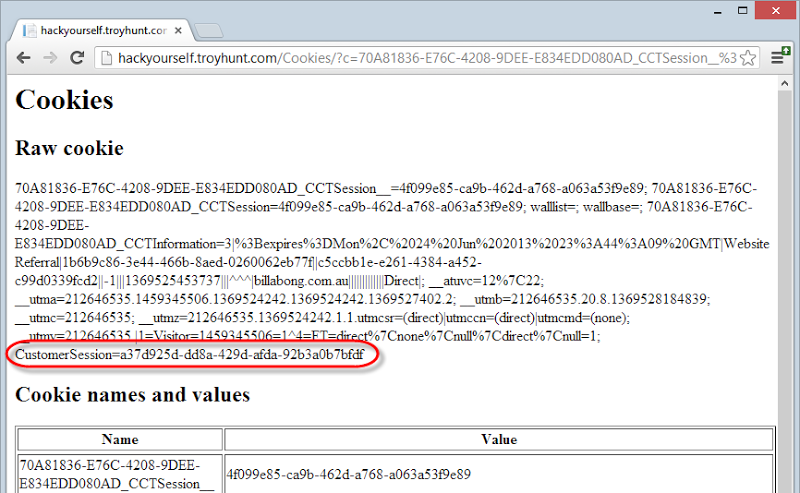
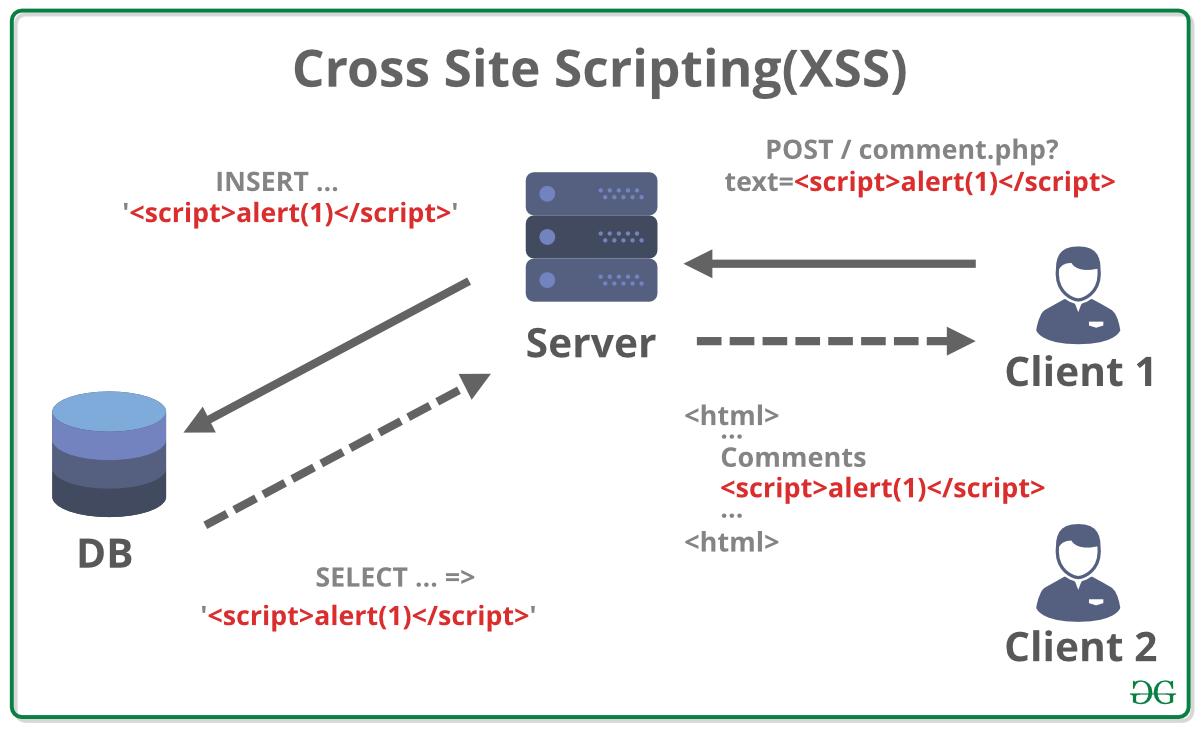
Cross-site scription (XSS) 101: What It Is, Why It's So Dangeruous, and How to Avoid It | Binary Studio
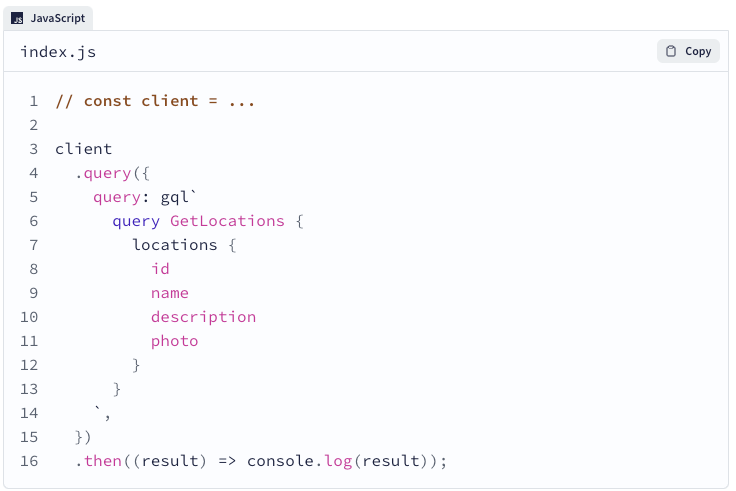
GitHub - leizongmin/js-xss: Sanitize untrusted HTML (to prevent XSS) with a configuration specified by a Whitelist

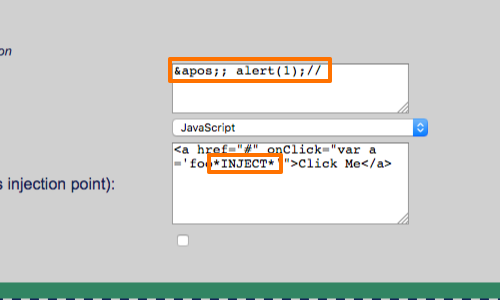


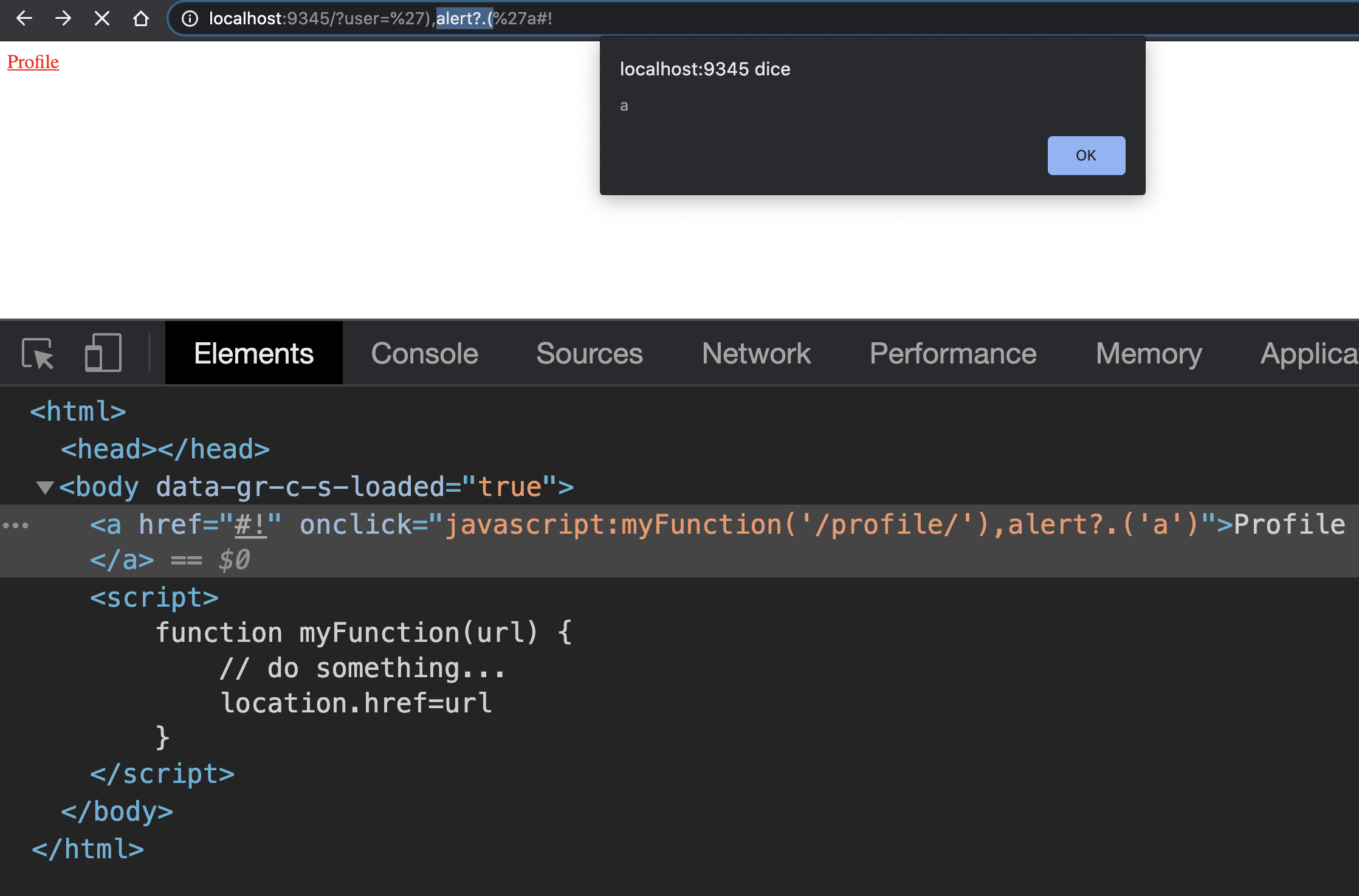
%20Attacks,%20Payloads%20And%20Bypass%20Technics.png)